Quantum-Safe Security Architecture
Traditional encryption algorithms will be vulnerable when quantum computers mature. PhantomVault employs a post-quantum cryptographic stack that protects your data against both current state-level adversaries and future decryption attempts.
- ✓ Kyber-768 PQE: Post-quantum key exchange mechanisms via `liboqs`.
- ✓ AES-256-GCM: Military-grade symmetric encryption for immediate, fortified protection.
- ✓ Argon2id KDF: Advanced key derivation with PBKDF2 fallback (≥500,000 iterations).
- ✓ BLAKE3 Merkle Trees: Highly efficient O(log n) cryptographic proofs of data integrity.
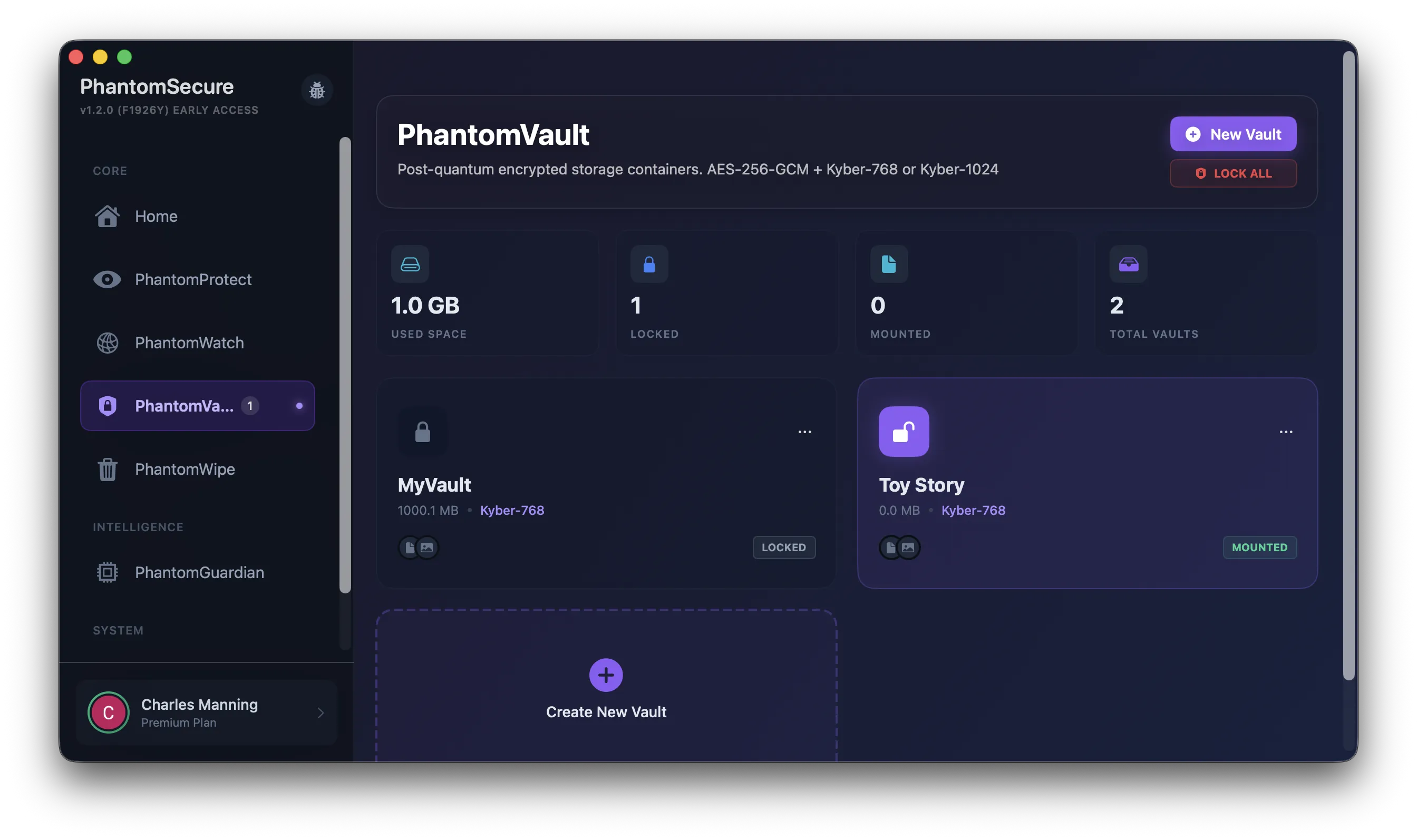
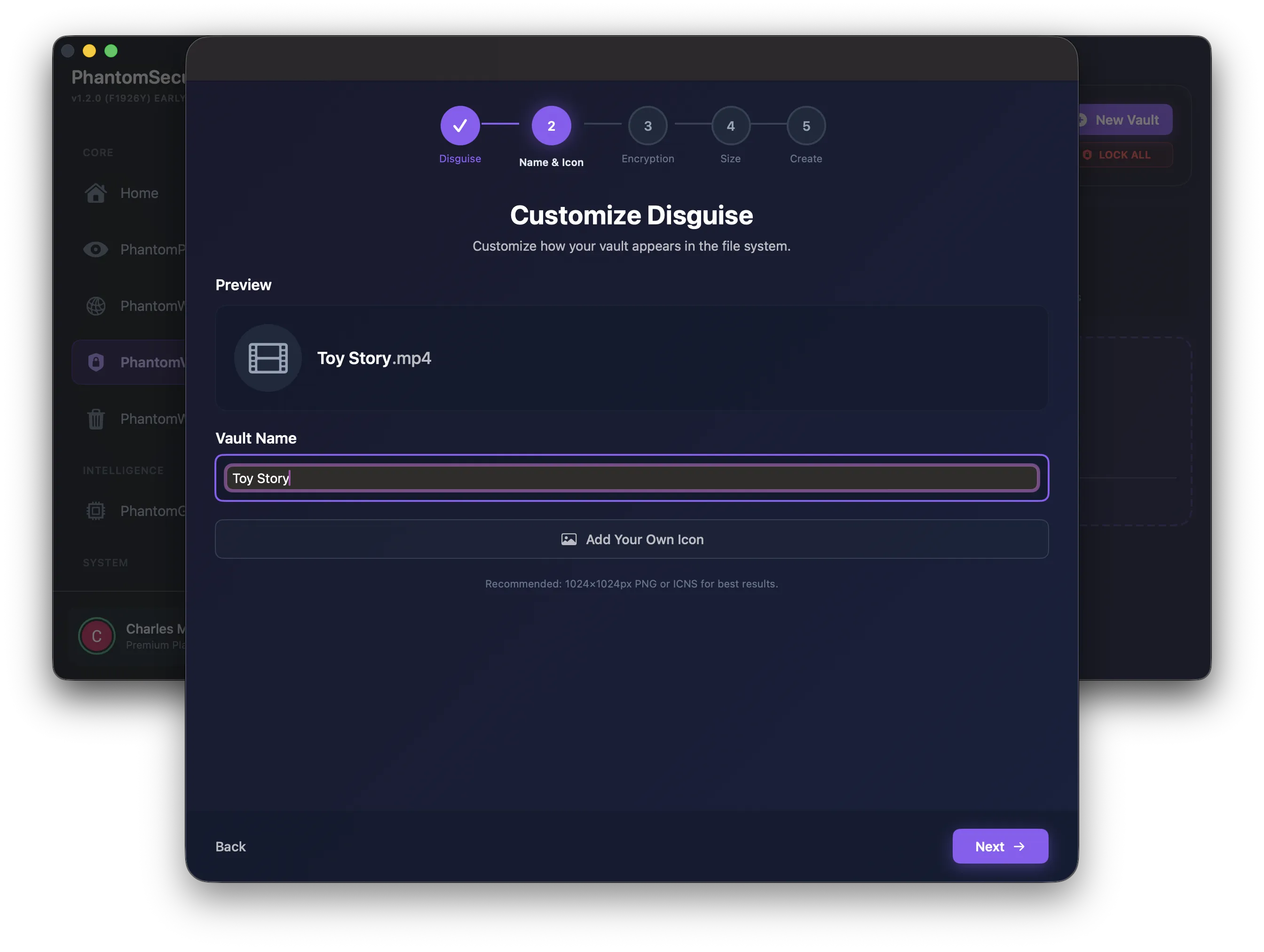
Plausible Deniability & Hidden Volumes
A cornerstone of PhantomVault is its advanced implementation of plausible deniability. Create a single vault that contains an outer decoy volume and up to 5 completely hidden inner volumes—perfect for high-risk, hostile environments.
- ✓ Steganographic Disguises: Vaults can structurally integrate and disguise as common media like `.mp4` or `.pdf`.
- ✓ Nested Volumes: Multiple completely separate passwords unlock entirely different hidden volumes.
- ✓ Duress Password: Instantly and silently trigger a cryptographic wipe if coerced.
- ✓ Dead Man's Switch: Auto-destruct vaults if not unlocked within a predefined period.
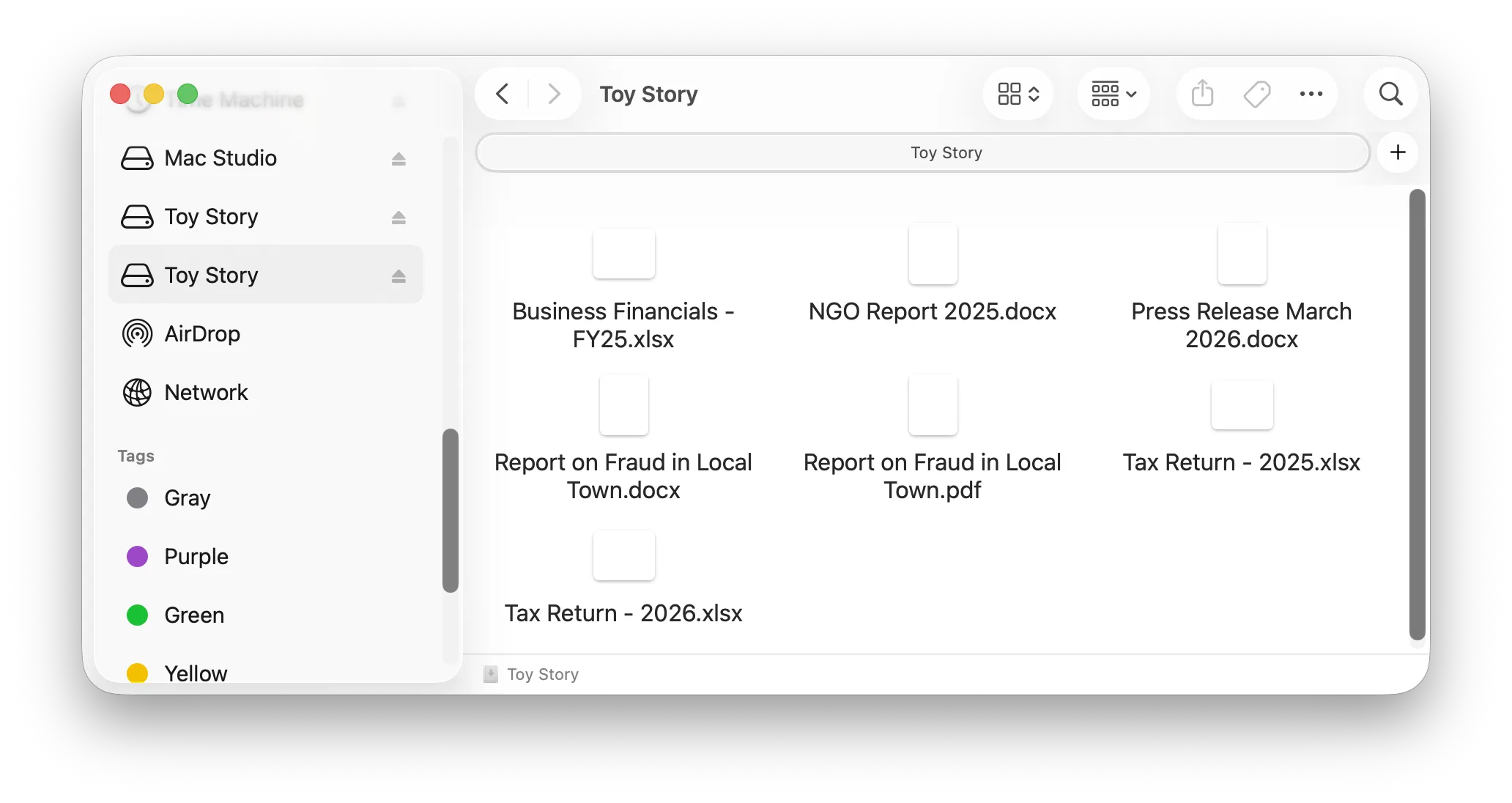
Anti-Forensics & Seamless Integration
Built exclusively for macOS 26 and Apple Silicon. Thwart advanced forensic analysis tools with extreme structural discipline, eliminating recognizable file footprint patterns, while maintaining a perfectly native Finder experience.
- ✓ FSKit Finder Integration: Integrates directly into the macOS File Provider domain without legacy volume mounting or Full Disk Access.
- ✓ Uniform Block Structure: Forces 4096-byte blocks to mathematically eliminate recognizable size correlation attacks.
- ✓ Pattern Obfuscation: Randomizes timestamps (±30 days jitter) and allocates fake blocks to hide the true payload.
- ✓ Constant-Time Operations: Prevents cache timing and memory residue attacks using C11 atomic fences.